Recent Waves of Phishing Attacks Overpowering 2-factor Authentication
Phishing attacks are still a leading attack vector for threat actors globally, & are evolving in prevalence & sophistication given work-from-home models
Executive summary
- Real-Time Authentication Phishing Kits implement a Man-in-the-Middle attack technique, allowing threat actors to obtain a live Office365 user session.
- Conditional Access rules applied to the Office365 tenant are a powerful and effective tool to mitigate this risk by only allowing trusted devices to connect.
- Sygnia’s recommendation is to proactively hunt for unauthorized access to Office365 accounts and any anomalous activities to detect breaches in your tenant.
Why two-factor authentication is no longer enough
Phishing campaigns have always been, and still are a leading attack vector for threat actors around the world. On top of that, with the new work-from-home model, phishing attacks have evolved in prevalence and sophistication. These attacks rely on human error and are used in campaigns to achieve a wide range of objectives, from credential theft to infiltration and mass infection of a target network.
Generally, implementing Two-Factor Authentication (2FA) is an adequate method for enhancing user security, and over the past two years has become common practice across organizations as part of the growing awareness of cyber threats. However, as security advances, so does the threat landscape, and attackers have been using tools that allow them to overcome standard 2FA solutions. Real-Time Authentication Phishing Kits implement a Man-in-the-Middle attack technique allowing threat actors to obtain a live user session when their target attempts to access a resource. While Real-Time Authentication Phishing Kits are not a new attack tool, their popularity and variations have increased, in part due to the growth in 2FA implementation.
A rise in number of campaigns using phishing kits
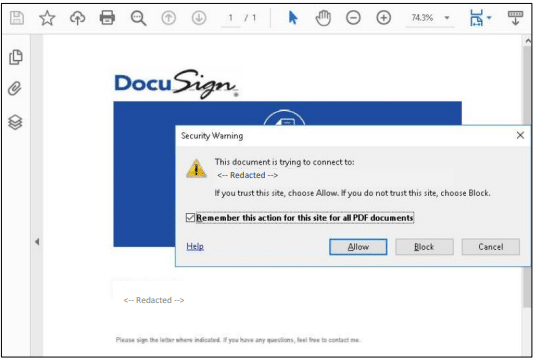
Over the past months, Sygnia has observed an increase in the number of phishing campaigns that utilize a Man-in-the-Middle technique to overcome 2FA. A recent and still active campaign, traced back to at least May2021, has compromised hundreds if not thousands of organizations. This campaign spreads phishing e-mails to unsuspecting users with a PDF attachment disguised as a request from DocuSign. When users open the PDF attachment, they are redirected to a phishing landing site, where they are prompted to login using their Office365 account. As the session is proxied through the threat actor server, once the user inputs their account name, password and 2FA code, the threat actor can initiate a live session, impersonating the victim and accessing any resource available to the account (Mailbox, SharePoint, etc.). Using this method, threat actor scan easily extract sensitive data and information from the account or attempt to commit financial fraud by transfer of funds to an external account.
What can be done?
With migration to the cloud, organizations must implement additional security measures to protect theirOffice365 accounts. Office365 allows implementation of their Conditional Access tool on AzureAD accounts, enforcing various rules and conditions for resource access requests. Through the implementation of Conditional Access, authorization can be managed based not only on credentials, but on multiple criteria such as IP addresses, specific devices, and more, thus achieving an additional layer of security. Just as firewall rules allow or block traffic based on predetermined rules, Conditional Access enhances Office365 security. Sygnia urges organizations to implement Conditional Access as part of their Office365 security architecture and manage the devices and locations from which resources are accessible. Any segment of an organization’s architecture that is not inspected and controlled leaves room for threat actor abuse.
Recommendations & Action items
Configure Conditional Access rules to enhance the Office365 tenant security
- Allow access to Office365 resources only from trusted devices and IP addresses
- Configure rules tailored for the different resources in the tenant
Proactively Hunt for:
- Unauthorized access to Office365 accounts specifically “Impossible Travel” cases
- Suspicious emails received from spoofed sources
- Emails including suspicious attachments (for example attachments with a double extension or documents that contact irregular domains)
- Emails embedding suspicious URLs

By clicking Subscribe, I agree to the use of my personal data in accordance with Sygnia Privacy Policy. Sygnia will not sell, trade, lease, or rent your personal data to third parties.