We stop at nothing to fortify our clients’ defenses so they can stay secure in the face of any and all cyber threats.

Eradicating A Persistent Attacker
An advanced threat actor attacked the client. The threat actor gained domain admin privileges over the network, including access to critical servers and backups.

Log4J Attack Contained In Minutes
The client had previously engaged Sygnia to contain and eradicate an attacker, including deployment of Sygnia’s Advanced Monitoring for post-breach surveillance.


Data Breach Remediated and Resilience Enhanced
Sygnia was called in to respond to the breach. A Sygnia IR team fully identified the entry point and lateral movement vectors of the attacker.

Stopping A Dangerous Supply Chain Attack
Sygnia performed a forensic investigation that uncovered the full attack scope, timeline, and methods.

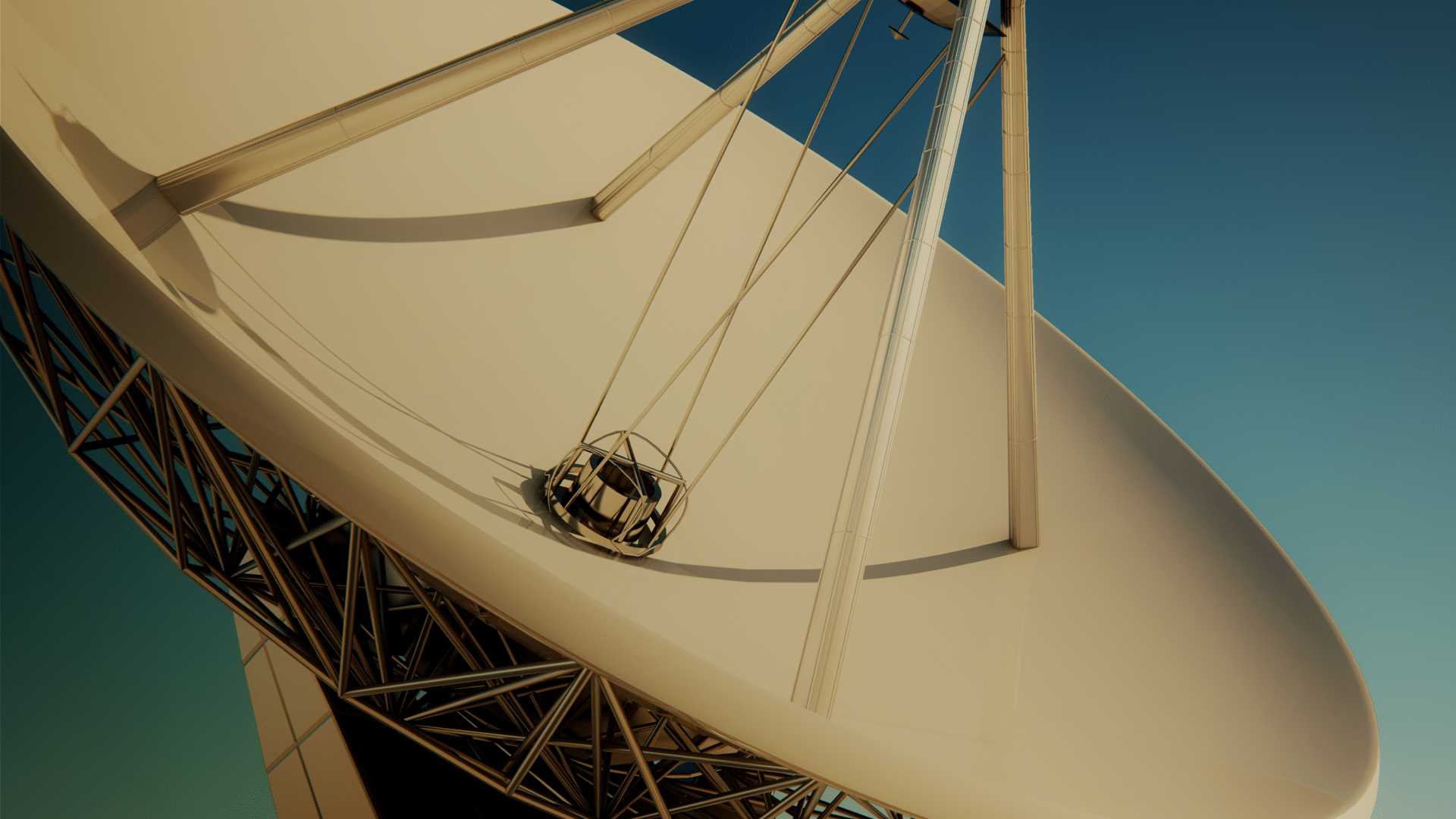
Securing A Port’s Crane and Container Management System
24 cyber- attack scenarios were developed and executed to test the port’s defenses against the ‘best practices’ commonly used by attackers when targeting similar infrastructure.

Defeating Multiple Simultaneous Attacks on a CSP
Sygnia was engaged to provide incident response services. Sygnia’s IR team immediately launched multiple workstreams to contain the attack and return operations to normal as quickly as possible.